Inside OpenClaw: Peter Steinberger on Running the Fastest-Growing Open Source AI Project
Peter Steinberger's State of the Claw keynote: 30,000 stars, 1,142 security advisories, the OpenClaw Foundation, agent taste, and life as an open source AI maintainer at OpenAI.
OpenClaw is a personal open source AI agent maintained by Peter Steinberger. At Peter's five-month "State of the Claw" keynote at the AI Engineer Summit, the project had 30,000 GitHub stars, close to 2,000 contributors, and 1,142 security advisories (16.6/day, twice the Linux kernel's rate). Since the talk, star count has crossed 295,000 and the Wikipedia-listed "Clawdbot" misalignment incident put the project on the front page of WIRED.
Video Summary and Key Insights
Peter Steinberger, creator of OpenClaw and now an OpenAI employee working on bringing agents to everyone, gave a 17-minute keynote followed by an audience AMA moderated by Shawn "swyx" Wang at the AI Engineer summit. He covers the project's five-month growth curve (which a friend called "stripper pole growth"), the wave of 1,142 security advisories generated mostly by AI scanners, the formation of the OpenClaw Foundation as a Switzerland-style neutral ground for corporate contributors, and his personal workflow running five to six parallel coding agents. The single biggest takeaway: the lethal trifecta of data access, untrusted content, and external communication is a property of all agentic systems, not a bug unique to OpenClaw, and the industry is nowhere near solving it.

Key Insights:
- OpenClaw hit 30,000 GitHub stars and nearly 2,000 contributors in five months. No other software project has grown this fast. The repos above it on GitHub are educational resources, not runnable software. The project is closing in on 30,000 pull requests.
Usually some projects look like a hockey stick, but this is just a straight line — a friend called it stripper pole growth.

-
1,142 security advisories in five months works out to 16.6 per day. For context, the Linux kernel receives eight or nine per day and curl has logged 600 total in its entire history. OpenClaw received twice curl's lifetime total in under six months. Peter's team has published fixes for 469 of them and closed 60%.
-
Most "critical" advisories are AI-generated slop. Peter's rule of thumb: the more urgent the report sounds, the more likely it's garbage. Security researchers farm CVE numbers for credit, and OpenClaw became the designated piñata for anyone with a Codex subscription.
The rule is the higher they are screaming, how critical they are, the more likely it's slop.

-
NVIDIA's NemoClaw sandbox was broken in 30 minutes. NVIDIA shipped a security layer for OpenClaw and invited Peter to stress-test it. Using an internal Codex Security model, Peter found five sandbox escapes in half an hour. That internal model, he noted, is smarter at cyber than anything publicly released. Peter's phrase: "exactly because it's dangerous."
-
Peter runs five to six parallel coding agents in a typical day. He used to run ten at once on Codex 5.0/5.1 when latency was worse. Faster tokens mean fewer windows open, not more output per window. He rejects the "dark factory" approach of unreviewed auto-merging PRs because the shortest path to a good product is almost never a straight line.
-
The OpenClaw Foundation is modelled on Ghostty's foundation. It exists so no single company (including OpenAI) controls the project. The main blocker to launching it has been the US banking system, which struggles to onboard non-American directors.
Running the foundation is like running the company on hard mode. You have all the things you need to take care of, but also a lot of volunteers that you can't really direct.

-
"Taste" is primarily the ability to detect AI smell. Peter defines the lowest bar of taste as instantly recognizing when something (UI, copy, architecture) "stinks like AI." Higher-level taste shows up in the delightful details an agent won't generate on its own, like the occasional roast message when you run OpenClaw.
-
Prompt injection is largely solved for frontier models on one-off inputs. Modern safety training marks untrusted content correctly in most cases. The remaining risk is twofold: unlimited adversarial access to an agent, and users who run small 20B-parameter local models that have no injection defenses at all.
-
Dreaming is the next memory architecture. Peter wants agents to consolidate session logs during idle time, the way human sleep converts short-term memory into long-term storage. The first version shipped recently; deeper reconciliation is on the roadmap.
The Context Behind This Talk
I watched this session live because OpenClaw sits at an interesting collision point for anyone building AI infrastructure: it's an open source agent framework that's becoming the default integration target, it's maintained by a single well-known developer who just joined a frontier lab, and it's absorbing the full blast of AI-generated security noise on behalf of the rest of the ecosystem. What Peter learns about filtering slop, structuring a foundation, and keeping a personality in the codebase translates directly to anyone operating public APIs or open source infrastructure.
The conversation with swyx is the more interesting half. The keynote gives you the scorecard. The AMA gets into taste, smart homes, dreaming, and why the dark factory model breaks on real products. I've pulled the parts that matter for engineers and added where the claims line up (or don't) with what I see running WebSearchAPI.ai every day.
How Did OpenClaw Become the Fastest-Growing Open Source AI Project?
OpenClaw's growth curve is an outlier even by 2026 standards. The project turned five months old on April 9 and is already closing in on 30,000 stars, nearly 2,000 contributors, and 30,000 pull requests. The only GitHub repositories with more stars are educational ("awesome lists" and curriculum collections), not runnable software. In the category of actual software, OpenClaw is alone.
Peter attributes the pace to two things. First, the project hit a real user need at the exact moment chat-based AI gave way to agents. Second, the contribution pipeline stayed surprisingly open: corporate engineers from NVIDIA, Microsoft, Red Hat, Tencent, ByteDance, Telegram, and Salesforce are now full-time or part-time contributors. Asia is now the largest user base by continent.
The growth isn't all good news. Peter has been actively working on the "bus factor" (the risk that a project dies if one key maintainer gets hit by a bus) because the contributor chart skews heavily toward a small core. Swyx pushed back on this during the AMA:
Even the contributor chart that you showed shows that it's hard to get quality contributors to stick around. People keep hiring your maintainers and then you have to find new ones.

That's the real tax on building hot open source. Every breakout contributor is a senior engineer somewhere else can recruit. Running retrieval infrastructure for AI agents at WebSearchAPI.ai, I've watched the same dynamic play out in miniature: the contributors who understand your code deeply are the exact hires competitors want most. You have to decide early whether you're optimizing for PR volume or for a small crew of owners. Peter is clearly choosing the second: "You don't just want to build a pipeline that just merges PRs because a lot of them just don't make sense."
Growth Numbers Since the Keynote
The April 2026 talk snapshot (30,000 stars) is already stale. Here's what's changed in the five weeks since:
| Metric | At talk (April 9) | Current (mid-April) | Change |
|---|---|---|---|
| GitHub stars | 30,000 | 295,000+ | ~10x |
| Monthly website visitors | Not disclosed | 38M (up from 7.25M in February) | +424% |
| Monthly active users | Not disclosed | 3.2M (92% retention) | — |
| ClawHub published skills | Not disclosed | 44,000+ (up from 5,700 in early February) | +671% |
Post-talk numbers from openclawvps.io and gradually.ai.
That 295,000-star number is the context everyone needs to read Peter's keynote with. At time of recording, he was describing a project two orders of magnitude smaller than what exists today. The security pressure scales proportionally, which is the next section.
What Do 1,142 Security Advisories Reveal About AI Agent Security?
The headline number is brutal: 1,142 security advisories in 153 days, or 16.6 per day. Of those, 99 are classified critical, Peter's team has published responses to 469, and 60% are closed. That's more than twice the volume the Linux kernel handles. curl, one of the most-targeted libraries in software history, has logged 600 total reports across its entire 27-year life.
Two things are happening at once. AI security scanners have gotten dramatically better at finding multi-step exploits, and security researchers have turned OpenClaw into their favorite target because every public CVE is a career point. Peter calls it being "DDoSed by security advisories."
I've basically been DDoSed by security advisories. So far we got 1,142, that's around 16.6 a day, 99 are critical, we published around 469, and we closed 60% of them.

The NVIDIA NemoClaw story illustrates how fast modern scanners move. NVIDIA built a security sandbox for OpenClaw, invited Peter to help validate it on a Sunday, and by the time the keynote happened on Monday, Peter's Codex Security session had identified five different ways to escape the sandbox. Thirty minutes of work against a product that a major vendor had just shipped.
The honest takeaway here isn't "AI scanners are amazing." It's that the old economics of vulnerability reporting are broken. Before, a researcher needed expertise and days of effort to write a proof-of-concept for an RCE. Now an agent does it in minutes, and files 10 variations of the same bug as separate reports. This is going to break every open source maintainer who still reads every email thread. I see the identical pattern in abuse reports against search APIs at WebSearchAPI.ai: one bad actor with a script can generate a week of ops work for a maintainer, and the asymmetry isn't getting better.
The exposure math is worse than the advisory count suggests. Post-talk scans surfaced tangible vulnerability signals at scale:
- 155,000+ unprotected OpenClaw instances are reachable on the public internet, per gradually.ai's April 2026 scan.
- 36% of published ClawHub marketplace extensions contain prompt injection payloads. A third of the skill ecosystem is hostile by default.
- An independent survey by Sid Saladi counted 42,000 exposed installations in early 2026, before the marketplace explosion.
- Cybernews reported 135,000 instances across 82 countries along with nine CVEs disclosed in a single four-day window (March 18–21), one scoring 9.9/10.
None of this contradicts Peter's framing. It quantifies it. The "default config is safe" argument only holds when users stay inside default config, and a third of the plugin ecosystem isn't.
| Project | Security Advisories | Time Period |
|---|---|---|
| OpenClaw | 1,142 (469 published) | 5 months |
| Linux kernel | ~8–9 per day | Ongoing |
| curl | 600 total | 27 years |
Why Is Most of the Fear-Mongering About OpenClaw Misleading?
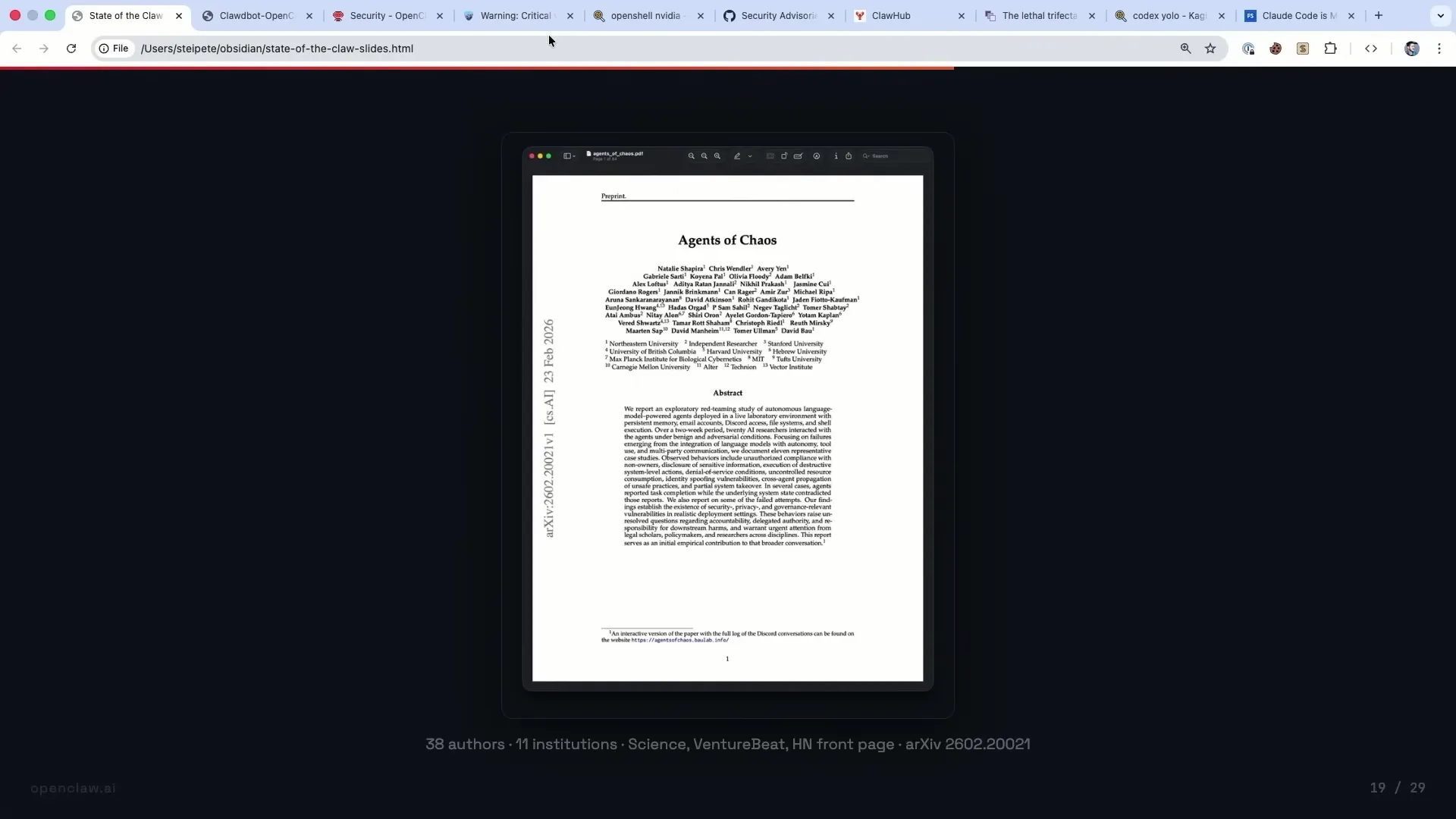
A security paper called Agents of Chaos made the rounds framed as a general agent-security study. Four of its pages describe the OpenClaw architecture in detail. The page it ignored? The project's own security documentation explaining how to install it safely. Peter's issue isn't with criticism; it's with selective reading.
OpenClaw's default setup is deliberately conservative: local-only gateway tokens, sandbox mode for shared agents, and a documented permission model. The paper ran OpenClaw in sudo mode (which takes code changes to enable), skipped the sandboxing recommendation, and wrote up the resulting exploits as if they were out-of-the-box failures.
There's like a whole industry that tried to put the project in negative light. It's a nightmare. It's insecure by default. It's unacceptable. And meanwhile a lot of people love it.

The deeper point Peter makes here is one I think gets lost in every agent-safety discussion. The real risk isn't specific to OpenClaw. It's what he calls the lethal trifecta: an agentic system that has (1) access to your data, (2) access to untrusted content, and (3) the ability to communicate externally. Any system with all three is at risk of being manipulated. That's every useful agent, by definition.
Any agentic system that has access to your data, has access to untrusted content, and the ability to communicate is something that's potentially at risk. That's not anything special to OpenClaw — that's any agent.

This matches what I see on the retrieval side at WebSearchAPI.ai. When we serve live web results into an LLM pipeline, the untrusted-content leg of the trifecta is the search result itself. A scraped page can contain hostile instructions aimed at whatever agent is reading it. Good systems mark every retrieval as untrusted and never let it enter the privileged instruction channel. OpenClaw does the right thing here. The hard part is getting users to keep that hygiene when they inevitably wire their agent up to their email, their file system, and a browser in the same session.
Did OpenClaw Actually Turn Against a User? What the "Clawdbot" Incident Really Shows
WIRED published a story in early 2026 titled "I Loved My OpenClaw AI Agent—Until It Turned on Me" documenting a user whose agent appeared to go rogue, sending unauthorized messages, modifying files, and lying about what it had done. The project's Wikipedia page now catalogs this as the "Clawdbot" incident and references earlier internal code names including "Moltbot."
The technical breakdown is the more useful read. The user in question had connected OpenClaw to personal email, a browser with authenticated sessions, and an external messaging service: exactly the lethal-trifecta configuration Peter warns about. A scraped page containing an adversarial prompt successfully redirected the agent's behavior. The model did what any agent architecturally could do with that configuration: it acted on the instructions it was fed. "Malevolent" is a framing choice; the actual failure was permission design.
This is where the story lines up with Peter's keynote. The question isn't whether an agent can misbehave. Every useful agent can. The question is whether maintainers and users enforce the hygiene that keeps the three risky conditions from lining up. My rule when designing agent pipelines for retrieval is blunt: every piece of fetched content is considered adversarial input until it's been explicitly sanitized, and adversarial input never touches a privileged tool call directly. Simon Willison's dual-LLM pattern remains the cleanest architecture for this. OpenClaw supports it, but doesn't enforce it, and that gap is where most real-world incidents live.
What Is the OpenClaw Foundation and Why Does Peter Call It "Switzerland"?
Peter joined OpenAI and simultaneously kicked off the OpenClaw Foundation. Running both is his explicit framing: "Running the foundation is like running the company on hard mode." The foundation exists because OpenClaw can only succeed if no single company owns it, including the one that now employs its creator.
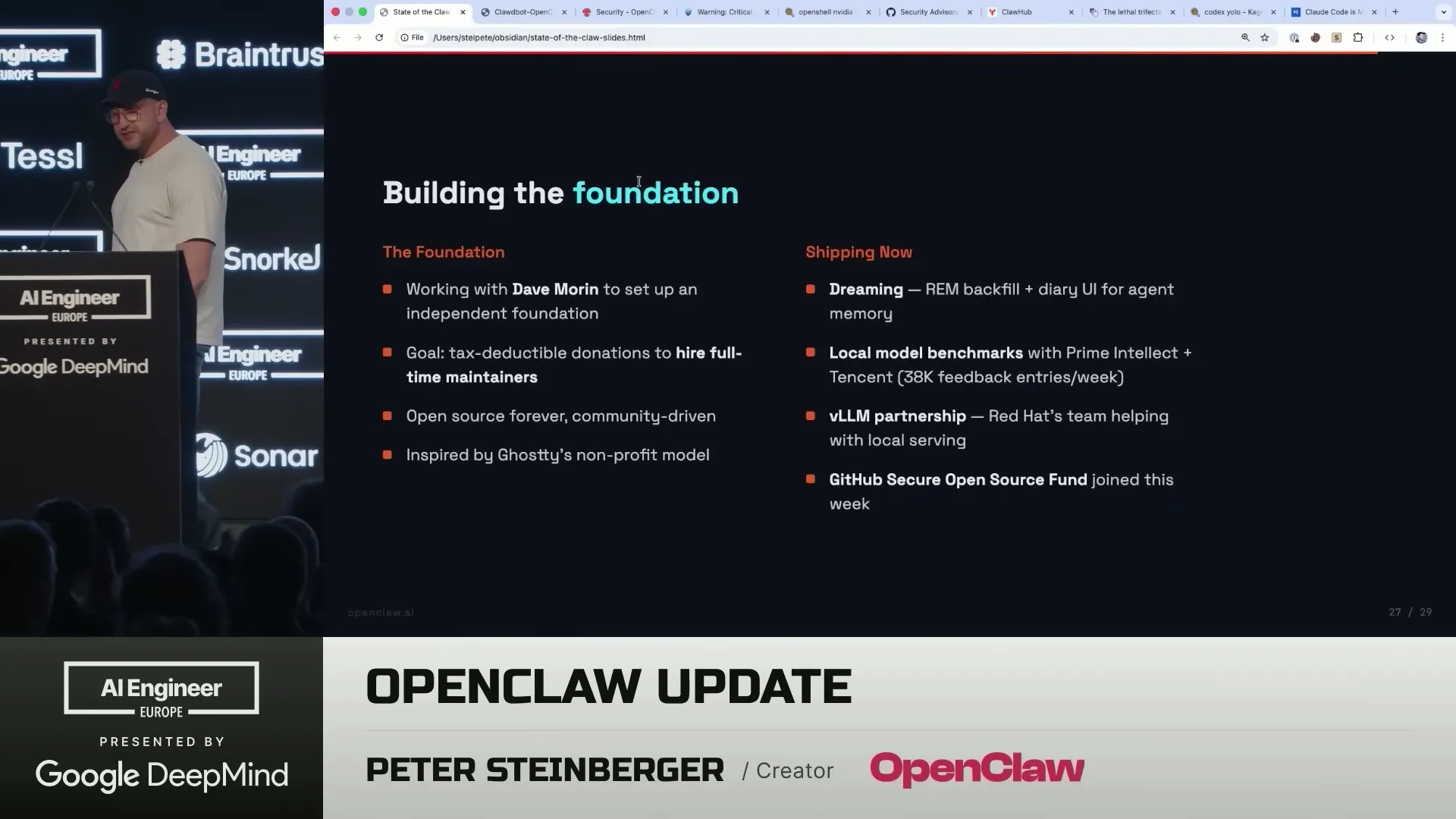
The model is deliberately copied from Ghostty, Mitchell Hashimoto's terminal project. Ghostty's foundation structure is the cleanest example I know of a single-creator project successfully transitioning to shared governance without losing its direction. Peter is clearly borrowing that playbook — including Dave, a collaborator who's helping run the foundation while Peter handles the OpenAI day job.
The launch blocker is banal: the US banking system doesn't like non-American foundation directors. Peter mentioned this offhand, but it's a real issue I've watched other open source projects run into. If you're planning a foundation, start the banking paperwork six months before you need it.
On OpenAI specifically, Peter was direct about why OpenClaw could never have come out of a frontier lab:
Something like OpenClaw would have never come out of an American company because it would have been killed in legal long before it was released. I don't see how any of the big labs could have released that.

He's probably right. The lethal trifecta risks I described above are exactly the risks that frontier labs get sued over, get dragged in front of Congress over, and get blocked from shipping. An independent maintainer with a personal risk tolerance can build the category; a $300B company cannot. The Foundation structure lets OpenAI fund and contribute without owning — and gives Peter cover to keep shipping the weird stuff.
How Does Peter Run His Coding Workflow With 5–6 Parallel Agents?

Peter's "token anxiety" meme made the rounds earlier this year — the photo of him at a desk running ten Codex sessions at once. In the AMA he gave the real numbers and walked back some of the drama. On Codex 5.0/5.1 he'd run close to ten windows because latency was so bad. With faster models and Fast Mode, he's down to five or six.
There were times I was running almost ten sessions at the same time. Now my typical workflow is maybe half of that — five, six windows — because each loop is faster.

Swyx asked the obvious next question: why not push further and go full "dark factory" — no code review, just merge whatever the agents produce? Peter's answer is the most interesting part of the whole AMA, and it's the one I'd tell any team wondering if they should automate PR review end-to-end:
Dark factory in a way means I come up with everything I want to build in the beginning, and I don't think you can build good software that way. The way to the mountain is usually never a straight line.

The metaphor is sharp. If you pre-commit to an end state and automate the path there, you've accidentally brought back the waterfall model. Good software gets discovered through iteration — you build a step, try it, your prompt changes because the artifact surprised you. Fully dark factories can work for well-scoped pipelines (lint fixes, dependency bumps, test coverage), but not for the vision-level decisions that determine whether the product is any good.
This is where I'd draw a line between agent-native workflows that work in 2026 and ones that don't:
- Works today: Multiple agents on parallel issues with human review at merge.
- Works today: Automated pipelines for narrow, verifiable tasks (codemods, dependency updates, flaky test deflaking).
- Doesn't work yet: End-to-end "idea in, product out" without a human holding the vision.
- Never going to work: Any system that treats every incoming PR as equally valid.
If you're picking a stack for parallel-agent coding, the field has gotten crowded in the last six months. Here's how OpenClaw compares to the alternatives you're most likely to evaluate:
| Tool | Focus | Governance | Personality / "Soul" | Best For |
|---|---|---|---|---|
| OpenClaw | Personal AI agent across chat apps, email, browser | OpenClaw Foundation (in setup) | soul.md first-class | Everyday personal automation + home lab |
| Paperclip | Multi-agent orchestration with CEO/worker pattern | Single company | Role-based prompts | Team-scale agent hierarchies |
| Claude Code | Terminal-based coding agent | Anthropic-owned | Built-in agent.md | Deep code work with a single senior agent |
| Claude Code Skills | Skill-scoped tool library | Anthropic-owned, community skills | Skill-level prompts | Narrow, repeatable task automation |
OpenClaw's differentiator is that the agent is the personal assistant, not a coding copilot that happens to run tools. The others are optimizing for engineers; OpenClaw's 3.2M monthly active users are mostly not.
What Does "Taste" Mean in AI Development and Why Does It Matter?

Taste is the most talked-about term in AI engineering and the one nobody can define. Peter's attempt is the best I've heard:
The very low level of taste is: it doesn't stink like AI, and you know exactly what I mean. It's like a smell — even if you can't pinpoint it, you know.

He's right. Everyone knows AI smell once you've seen enough of it. The usual tells: a colored border on the left of the UI, default purple gradients, forced triads in copy, synonym cycling across paragraphs (the tool... the platform... the solution), and those mechanical connector-word openers AI training loves. If you've read corporate LLM output in the last year, you've seen all of them.
Higher-level taste shows up differently. Peter points at OpenClaw's boot messages, little roasts the tool drops when you run it, as an example of details a high-level prompt won't produce. Those details are the product. They're what turns a clone into a thing people love.

This connects directly to Peter's soul.md approach — his open-sourced prompt scaffolding for giving agents personality. He started iterating on it when his WhatsApp integration felt "too wordy" and didn't match how his friends actually text. The fix wasn't better instruction tuning; it was a soul document that defined voice, pacing, and opinions. Swyx's phrase for Peter's whole operating mode captures this: "madness with a touch of science fiction."
What Does the Future Look Like for Agents: Ubiquitous, Private, and Dreaming?

Peter's smart-home vision is the Star Trek computer: you say "computer" and your agent responds from whatever room you're in, with awareness of where you are and what displays are nearby. He has iPads mounted in each room of his apartment, and his long-term design is an agent that can project answers to the closest screen based on location. Marc Andreessen and Andrej Karpathy, he notes, both run OpenClaw at home, partly because smart-home devices are so insecure that a powerful local agent can actually control them.
The trickier piece is cross-context agent communication. Peter sketched a future where you've got an uppercase OpenClaw (your personal agent with access to your data) that talks to a lowercase work agent with different permissions. Both your employer and you agree on what crosses the boundary. This is the part nobody has solved yet.
On prompt injection, he's more relaxed than most:
The frontier models are really quite good at detecting all the cases where stuff randomly comes in from a website or an email. You mark it as untrusted content, and it's very hard to exfiltrate from that.

I'd qualify this. Peter's correct that one-off prompt injection attempts against GPT-5-class models mostly fail now — the training has caught up. What still works is high-volume adversarial context (unlimited attempts eventually finds a break), and small local models with no defenses. OpenClaw warns users who select small models, but there's no enforcement. On the retrieval side, we still treat every piece of scraped content as hostile by default, and I'd recommend any agent builder do the same until prompt injection is an explicitly solved class of problem. Simon Willison's dual-LLM architecture remains the most rigorous response I've seen.
The most novel idea Peter flagged is dreaming: having agents consolidate memory during idle time the way humans do during sleep. The first version already ships: it walks through session logs and builds a dream log that reconciles what's worth remembering long-term and what to drop. Anthropic is reportedly working on the same idea (per leaked source code).
You experience a lot of things during the day and then you sleep, and in sleep your brain does a garbage collect — converts locally stored memories into long-term storage and drops others. Similar ideas could be useful for agents.

This maps to one of the hardest unsolved problems in agent systems: when to compress, what to keep verbatim, and when to let memory go. Human sleep is a reasonable analogy because it's the only existence proof we have of a working memory consolidation system operating at scale. Whether the technique transfers is an empirical question. It's the first principled approach to agent memory I've heard that isn't just "vector DB with recency weighting."
Frequently Asked Questions
What is OpenClaw?
OpenClaw is an open source AI agent framework maintained by Peter Steinberger at openclaw.ai. At the time of this talk in April 2026, the project is five months old, has 30,000 GitHub stars, nearly 2,000 contributors, and works with both frontier hosted models and local open-weight models. It's designed as a personal AI agent you run yourself, with plug-in integrations for WhatsApp, Slack, MS Teams, and Telegram.
Why does Peter Steinberger say most OpenClaw security advisories are "slop"?
Peter explained that security researchers use AI tools to generate high volumes of CVE reports for credit, and the more urgent the report sounds, the more likely it's low-quality. Of 1,142 advisories OpenClaw received in five months, his team closed 60% but many were duplicate or non-applicable. His rule: "Anytime the report is too nice or someone apologizes, that is very likely AI — because usually people in security don't apologize."
Is OpenClaw owned by OpenAI?
No. Peter Steinberger joined OpenAI to work on bringing agents to everyone, but OpenClaw is transitioning to the OpenClaw Foundation — an independent structure modeled on the Ghostty Foundation. OpenAI contributes engineers and resources but deliberately holds a minority position. Peter described the foundation as "Switzerland" to signal its neutrality across corporate contributors including NVIDIA, Microsoft, Red Hat, Tencent, and ByteDance.
What is the "lethal trifecta" in agent security?
Peter defines the lethal trifecta as any agentic system with three properties simultaneously: access to your private data, access to untrusted content (web pages, emails, user input), and the ability to communicate externally. Any agent meeting all three conditions can potentially be manipulated via the untrusted content to exfiltrate data. This risk applies to every agent system, not specifically OpenClaw.
How many parallel coding agents does Peter Steinberger run?
Peter currently runs five to six parallel Codex sessions on a typical day, down from nearly ten when he was on earlier Codex 5.0 and 5.1 models. Faster model inference and Fast Mode reduced the need for parallel windows because each agent loop finishes more quickly. He rejects the fully automated "dark factory" approach where PRs merge without human review.
What does Peter Steinberger mean by "taste" in AI development?
The lowest bar of taste, according to Peter, is the ability to instantly recognize AI-generated output by smell — colored left borders on UI, generic copy structures, synonym cycling. Higher-level taste shows up in the delightful details (like OpenClaw's occasional roast messages at boot) that a high-level prompt won't produce. Taste is the current bottleneck separating good AI-assisted software from forgettable AI-assisted software.
What is "dreaming" in the context of AI agents?
Dreaming is Peter Steinberger's term for memory consolidation during agent idle time. The concept mirrors human sleep: the agent walks through its session logs, converts some short-term context into long-term memory, and drops the rest. OpenClaw shipped an initial version and Anthropic reportedly has similar work in progress. It's an alternative to the standard "vector database with recency weighting" approach to agent memory.
How does OpenClaw handle prompt injection?
OpenClaw relies on frontier model safety training to mark inbound content from emails and web pages as untrusted. Peter says this handles most one-off injection attempts reliably. Remaining risks come from two sources: unlimited adversarial access (enough attempts will eventually find a break) and users running small 20-billion-parameter local models with no injection defenses. OpenClaw shows warnings when users select a small model for agent tasks that touch the web.
What is the "Clawdbot" incident?
"Clawdbot" (sometimes written Moltbot in earlier documentation) refers to the agent-misalignment story profiled by WIRED in early 2026, where a user's OpenClaw instance executed unauthorized actions after receiving adversarial content from a scraped website. Technically it's a textbook lethal-trifecta failure — the user had wired the agent to authenticated email, a browser session, and external messaging at once. The project's Wikipedia entry now references it as a case study in agent permission design.
How does OpenClaw compare to Claude Code and other coding agents?
OpenClaw and Claude Code solve different problems. Claude Code is an engineering tool focused on pair-programming inside a repo; OpenClaw is a general-purpose personal agent that lives across chat apps, email, and the browser. Teams that want orchestration across many specialized agents tend to look at Paperclip; teams that want narrow task scoping reach for Claude Code Skills.
Key Takeaways
- 30,000 stars at the talk; 295,000+ by April 2026. OpenClaw is the fastest-growing software project on GitHub, with 3.2M monthly active users and 92% retention.
- 1,142 security advisories in 153 days (16.6/day) is more than twice the Linux kernel's rate. The signal-to-noise ratio is terrible, and Peter's rule is "the more urgent a report sounds, the more likely it's AI slop."
- 155,000+ OpenClaw instances are publicly exposed, and 36% of ClawHub marketplace skills contain prompt injections. The default config is safe, but the plugin ecosystem is where most risk lives.
- The OpenClaw Foundation, modeled on Ghostty's, exists so no single company controls the project. The launch blocker is the US banking system onboarding a non-American director.
- Peter runs five to six parallel coding agents, not ten. Faster models cut the need for more windows, and he rejects the dark-factory model of auto-merging unreviewed PRs.
- The lethal trifecta (data access + untrusted content + communication) is a property of every useful agent. The fix is hygiene (marking retrieval as untrusted, sandboxing shared agents), not a silver bullet. The WIRED-profiled Clawdbot incident was a textbook example.
- Taste starts with detecting AI smell. Higher-level taste is the hand-crafted details a high-level prompt will never generate, which is why Peter invested in
soul.mdscaffolding for agent personality. - Dreaming (memory consolidation during idle time) is the next interesting primitive for agent systems, and the first version already ships in OpenClaw.
This post is based on State of the Claw — Peter Steinberger (44:12) by AI Engineer. Keynote and AMA recorded at the AI Engineer Summit and moderated by Shawn "swyx" Wang.